AirTag privacy is a hot topic these days as more people start using Apple’s tracking device. In this blog post, we’ll explore how AirTags work and what you need to know to keep your privacy intact.

AirTag privacy
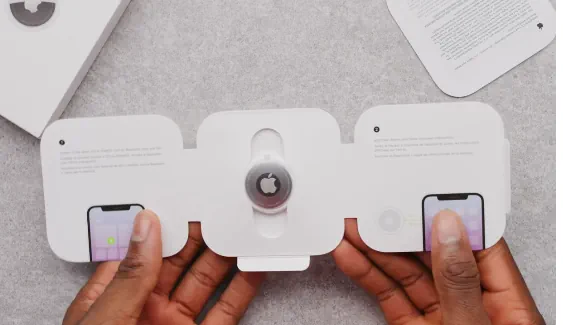
One of the major privacy concerns surrounding Apple’s AirTags is the potential for unauthorized tracking. While AirTags are designed to help you find lost items, the technology could be misused to track people without their consent. Apple has implemented features like “Unknown Accessory Detected” notifications to alert iPhone users if an AirTag that isn’t paired with their device is moving with them. However, this feature is currently limited to iOS users, leaving Android users more vulnerable to potential stalking.
Another issue is data security. AirTags use end-to-end encryption, meaning that only the owner of the AirTag can see its location. While this is a strong security feature, no system is entirely foolproof. If someone were to gain unauthorized access to your Apple ID, they could potentially access the location data of your AirTags. This raises questions about how secure your data really is, especially if you’re not diligent about maintaining strong, unique passwords for your accounts.
Also, there’s the concern of data collection and sharing. Apple states that AirTags do not store any location data on the device itself and that the location data is anonymized and encrypted. However, as with any device that uses location services, there’s always the question of how this data could be used or misused in the future. While Apple has a relatively strong track record on privacy, the increasing integration of AI and big data analytics in our lives makes it essential to stay vigilant about how our data is handled.
There are several other concerns about the privacy of AirTags. These are the most commonly discussed ones:
- Unauthorized Tracking: AirTags could be used to track people without their consent, potentially leading to stalking or other invasive behavior.
- Limited Non-iOS Support: Features designed to alert users of unauthorized tracking are currently optimized for iOS, leaving Android users more vulnerable.
- Data Security: While AirTags use end-to-end encryption, unauthorized access to your Apple ID could compromise the location data of your AirTags.
- Data Collection and Sharing: Although Apple states that AirTags do not store location data and that this data is anonymized, there are concerns about how this data could be used or misused in the future.
- False Positives: The “Unknown Accessory Detected” feature could potentially generate false positives, causing unnecessary concern or confusion.
- Battery Replacement Alerts: Since the battery is user-replaceable, someone could potentially remove and replace the battery to continue unauthorized tracking without the user’s knowledge.
- Dependence on Community Network: AirTags rely on the Find My network, which means other Apple devices around the lost AirTag help in its location. This raises questions about the extent of data sharing involved.
- Legal and Ethical Use: There are concerns about how AirTags could be used in legal cases, such as evidence in court, which opens up a host of ethical considerations.
- AI and Big Data Concerns: The increasing role of AI in data analytics and location tracking adds another layer of complexity to privacy issues.
- International Regulations: Different countries have different privacy laws, and how AirTags adhere to these varying regulations is a concern.
- Accessibility: Features like audible alerts are not universally accessible, potentially leaving some users, such as those who are hearing-impaired, at a disadvantage.
- Ownership Transfer: If an AirTag is sold or given to someone else, ensuring that all data is completely transferred or erased is a concern.
Privacy implications
Apple AirTags offer valuable tracking capabilities for lost items, but they raise privacy concerns, including the risk of unintended tracking if an AirTag is covertly placed in someone’s belongings. To address this, Apple has integrated safety features such as Separation Alerts and notifications for unfamiliar AirTags near you. While AirTags use the Find My network for location tracking, this data is encrypted and anonymous, but item ownership information can be accessed using NFC. Additionally, user-replaceable batteries and device registration have prompted privacy discussions. To mitigate these concerns, Apple provides educational resources and encourages responsible usage, while governments consider regulation in this evolving landscape, emphasizing the importance of both convenience and privacy awareness.
Data protection
Apple has implemented measures to safeguard user privacy. Location data shared within the Find My network is encrypted and anonymized, and anti-stalking features are in place to prevent misuse. Users should be aware of the privacy settings and follow responsible usage guidelines to ensure their data remains protected while benefiting from AirTags’ tracking capabilities.
Can other people see your AirTag?
Other people cannot see your specific AirTag’s location or any personal information associated with it. Apple has designed AirTags with privacy in mind. Here’s how it works:
- Location Privacy: The location of your AirTag is not visible to anyone except you, the owner, through the Find My app on your iOS device. It remains completely private.
- Anonymous Tracking: AirTags can utilize the Find My network, which allows them to communicate with other Apple devices nearby. However, this communication is done anonymously and securely. Other Apple device users won’t know they are helping to track your AirTag, and the data they transmit is encrypted.
- Item Ownership Information: If someone finds your lost item with an AirTag attached and wants to contact you, they can do so by tapping their NFC-capable smartphone to the AirTag. This will display a website with your contact information, but it doesn’t reveal your personal details to them directly. It’s a privacy measure to help you recover lost items without exposing your identity.
Personal security
User personal security is a crucial aspect when it comes to using Apple AirTags, as they are tracking devices that can be misused for harmful purposes.
Here are some important considerations for user personal security with Apple AirTags:
- Item Labeling: When you set up an AirTag, it’s important to label the item it’s attached to, especially if you’re using multiple AirTags. This labeling can help you identify the purpose of each AirTag and reduce the risk of misuse.
- Check for Unknown AirTags: Regularly check the Find My app on your iOS device to ensure that no unknown AirTags are listed as traveling with you. If you see an unfamiliar AirTag, follow Apple’s guidelines for what to do next, as it may be a tracking attempt.
- Disable Unwanted Notifications: You can disable notifications for “Items Detected” in the Find My app if you find them too frequent or unnecessary. However, it’s essential to strike a balance between convenience and personal security.
- Secure Personal Items: Ensure that the items you attach AirTags to are secure and not easily accessible to others. This is especially important for valuable items like wallets and bags.
- Education and Awareness: Educate yourself and those in your household about the potential risks associated with AirTags. Make sure everyone knows how to recognize and respond to security and privacy concerns.
- Report Suspicious Activity: If you suspect that someone is using an AirTag to track you or your belongings without your consent, report it to law enforcement. Apple provides resources to help law enforcement investigate such cases.
- Battery Replacement Awareness: Be cautious when replacing the AirTag’s battery. While it’s designed to be user-replaceable, ensure that you are the rightful owner of the AirTag, as unauthorized battery replacements can be a security concern.
- Privacy Settings: Familiarize yourself with the privacy settings for AirTags in the Find My app. You can enable or disable features like Precision Finding and the Find My network according to your preferences and security concerns.
- Trust Your Instincts: If something feels off or suspicious, trust your instincts and take appropriate actions. It’s better to be cautious than to disregard potential security risks.